As the vacation season of 2023 unfolded, it introduced not solely cheer and celebration but in addition a surge in Distributed Denial-of-Service (DDoS) assaults. This 12 months’s developments in DDoS assaults reveal a fancy and evolving risk panorama. From misconfigured Docker API endpoints enabling botnet supply to the emergence of NKAbuse malware exploiting blockchain know-how for DDoS assaults, the techniques and scale of those assaults have proven vital sophistication and diversification.
The 2023 vacation season assault panorama in Azure
In our monitoring of the assault panorama through the vacation season, we noticed a notable shift in a few of the assault patterns in comparison with the earlier 12 months. This transformation underscores the relentless efforts of malicious actors to refine their risk techniques and try to bypass DDoS safety methods.
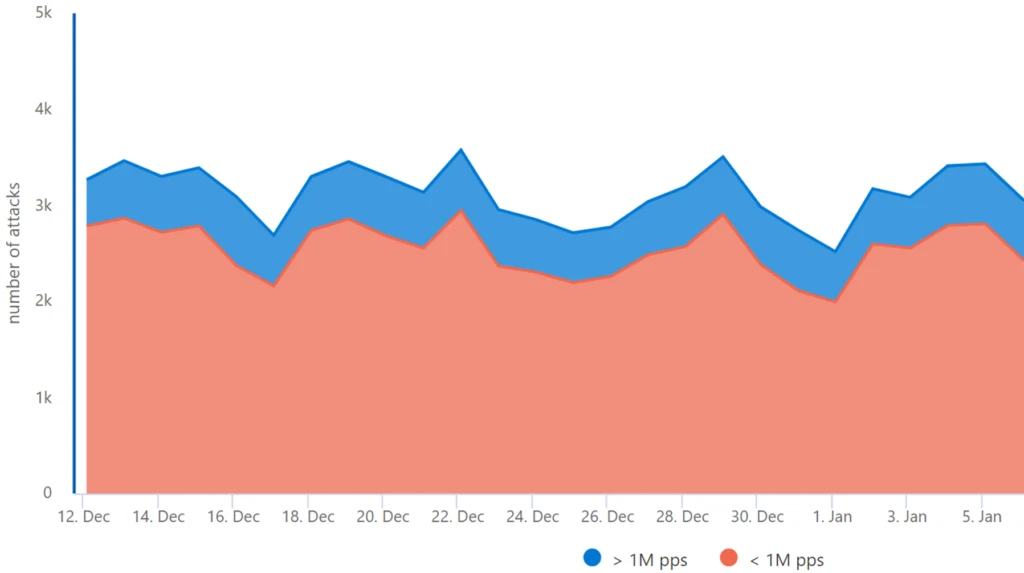
Day by day Assault Quantity: Azure’s strong safety infrastructure routinely mitigated a peak of 3,500 assaults every day. Notably, large-scale assaults, exceeding 1 million packets per second (pps), constituted 15%-20% of those incidents.*
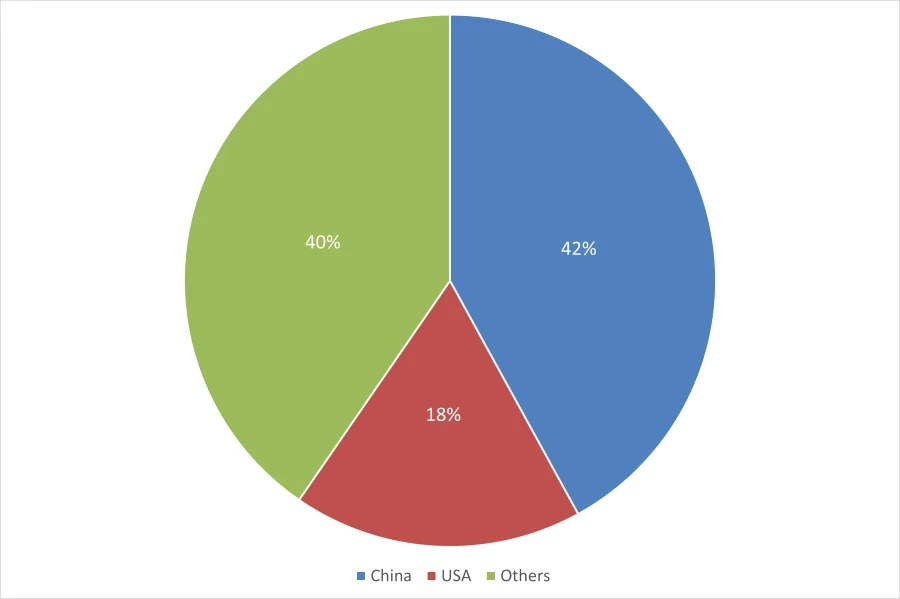
Geographical origins: A shift in assault origins was noticed, with the high two origin international locations being China with 42% of the assaults and the USA with 18%. All different international locations make up 40% of assaults.* This marks a change from the earlier 12 months, the place each international locations had been equally represented as the high two regional sources.
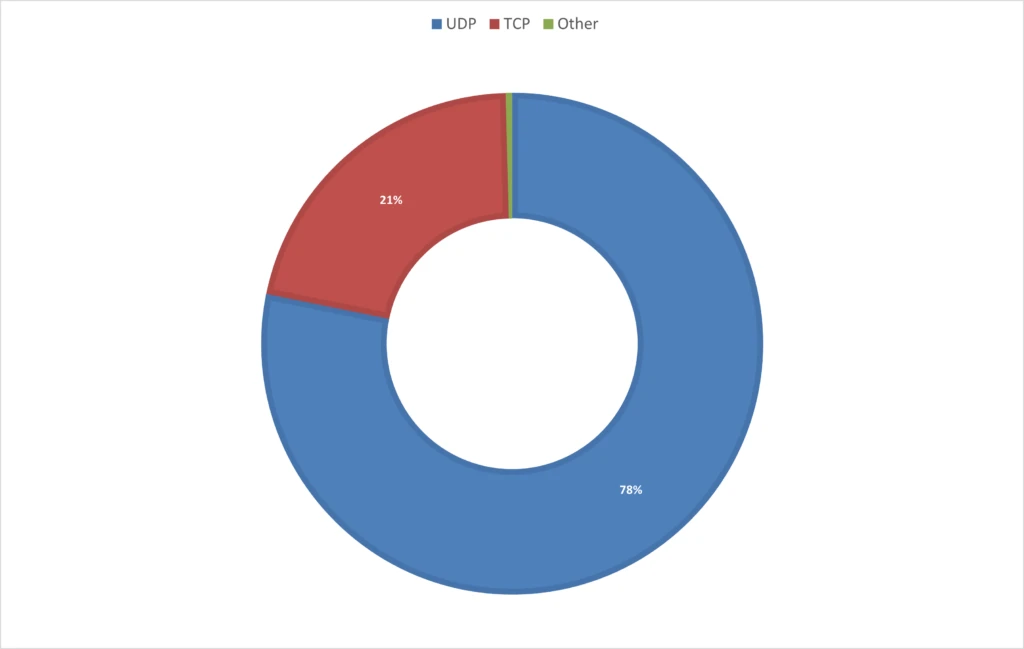
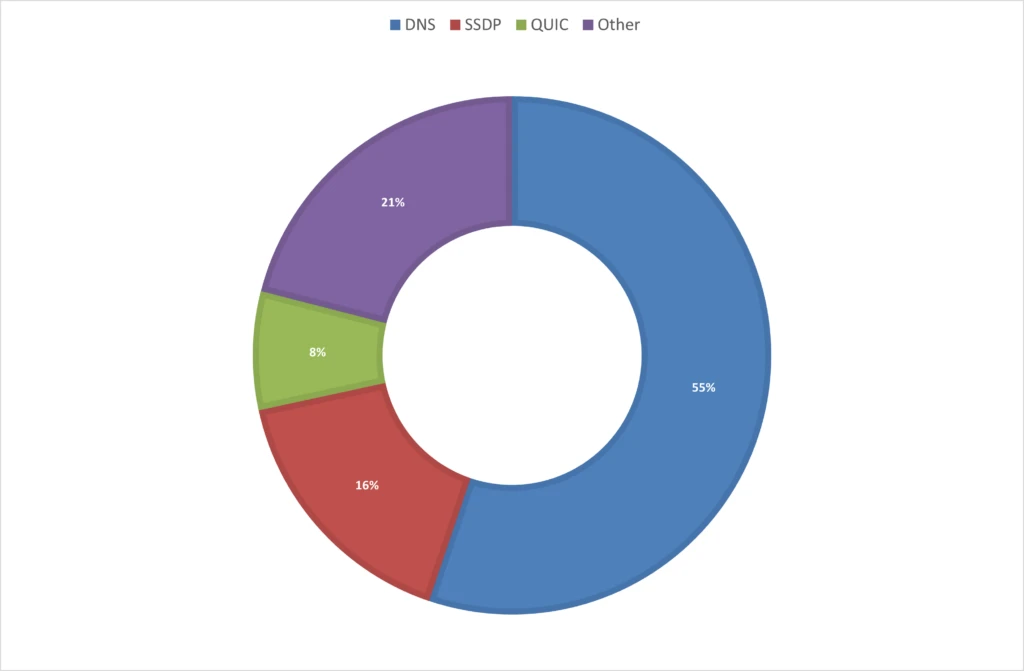
Assault protocols: The 2023 vacation season noticed a predominant use of UDP-based assaults, focusing on gaming workloads and net functions, accounting for 78% of the assaults. These embody UDP mirrored/amplified assaults, which predominantly leverage area identify system (DNS) and easy service discovery protocol (SSDP), in addition to fast UDP web connections (QUIC) for reflection functions. Notably, QUIC is rising as a extra widespread assault vector, both by reflection or by DDoS stressors that make the most of UDP port 443 randomly. This 12 months’s vacation season assault patterns distinction sharply with the earlier 12 months, the place TCP-based assaults dominated 65% of all assaults.*
Report-breaking assault: A staggering UDP assault, peaking at 1.5 terabits per second (Tbps), focused a gaming buyer in Asia. This assault, originating from China, Japan, the USA, and Brazil, was extremely randomized, involving quite a few supply IPs and ports, but was absolutely mitigated by Azure’s defenses.
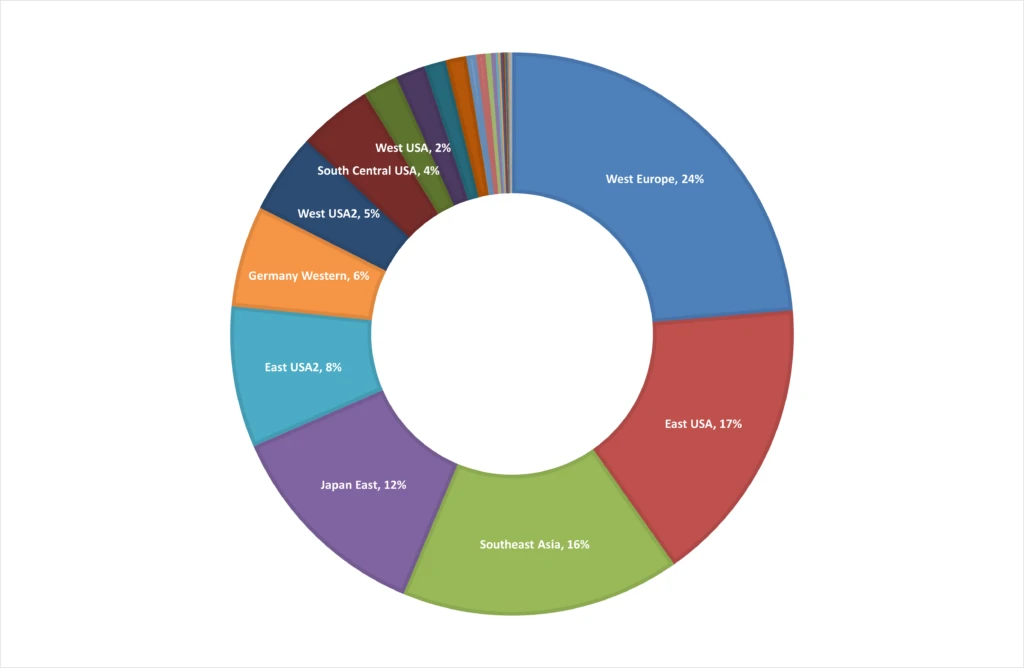
Botnet evolution: Up to now 12 months, cybercriminals more and more leveraged cloud assets, significantly digital machines, for DDoS assaults. This development continued to evolve through the vacation season, with attackers attempting to use discounted Azure subscriptions globally. From mid-November 2023 and till finish of 12 months, we monitored compromised account makes an attempt in 39 Azure areas, with Europe and the USA being the first targets, accounting for about 67% of those incidents.* Azure’s protection mechanisms efficiently neutralized these threats.
Contextualizing the risk
The 2023 DDoS assault developments in Azure mirror world patterns. Assaults are changing into politically motivated as we highlighted earlier final 12 months, fueled by geopolitical tensions.
The emergence of DDoS-for-hire providers, generally often known as “stressers” and “booters” stay common amongst attackers. These platforms, available on cybercriminal boards, have democratized the power to launch highly effective DDoS assaults, making them accessible to much less refined criminals for minimal prices. Latest years have seen an uptick within the availability and use of those providers, confirmed by worldwide regulation enforcement businesses by means of operations like Operation PowerOFF, which final 12 months in Could focused 13 domains related to DDoS-for-hire platforms. Regardless of these efforts, stressers proceed to thrive, providing a variety of assault strategies and energy, with some able to assaults as much as 1.5 Tbps.
Cloud energy: Combating the evolving DDoS threats
The rise of botnets at scale and DDoS-for-hire providers poses a major threat to on-line providers and enterprise operations. To struggle these threats, extra cloud computing energy is required to soak up the main wave of the assault till patterns might be recognized, spurious visitors diverted, and bonafide visitors preserved. When tens of 1000’s of gadgets represent an assault, the cloud is our greatest protection, because of the scale wanted to mitigate the biggest assaults. As well as, because of the world distribution of the cloud, nearer proximity helps to dam assaults closest to the sources.
Making certain strong safety
In an period the place digital threats are consistently evolving, making certain strong safety towards DDoS assaults has by no means been extra vital. Right here’s how Azure’s complete safety options are designed to safeguard your digital infrastructure.
DDoS Safety Service: With the excessive threat of DDoS assaults, it’s important to have a DDoS safety service like Azure DDoS Safety. This service gives always-on visitors monitoring, automated assault mitigation upon detection, adaptive real-time tuning, and full visibility on DDoS assaults with real-time telemetry, monitoring, and alerts.
Multi-Layered Protection: For complete safety, arrange a multi-layered protection by deploying Azure DDoS Safety with Azure Net Utility Firewall (WAF). Azure DDoS Safety secures the community layer (Layer 3 and 4), whereas Azure WAF safeguards the applying layer (Layer 7). This mixture gives safety towards numerous kinds of DDoS assaults.
Alert Configuration: Azure DDoS Safety can establish and mitigate assaults with out consumer intervention. Configuring alerts for lively mitigations can preserve you knowledgeable concerning the standing of protected public IP assets.

Azure DDoS Safety
Defend your Azure assets from distributed denial-of-service (DDoS) assaults.
2024: Rising towards DDoS threats
The 2023 vacation season has underscored the relentless and evolving risk of DDoS assaults within the cyber panorama. As we transition into the brand new 12 months, it turns into essential for organizations to boost and adapt their cybersecurity methods. This era needs to be a studying curve, specializing in fortifying defenses towards such DDoS assaults and staying vigilant towards new techniques. The resilience of Azure towards these refined DDoS threats highlights the vital want for strong and adaptive safety measures, not simply in defending digital property but in addition in making certain uninterrupted enterprise operations.
* Based mostly on inner knowledge

